With the continuous evolution of technology over time, we keep witnessing amazing stuff. Stuff that we never thought was possible. The world of technology and the Internet has grown up to become even larger than the real world. One of the major concerns which exist in the tech world is privacy and security that affects us significantly. The internet is administered through several remote servers. Several services host our data on cloud servers or their own servers to get us connected to the internet and use the specific tool or service. However, a lot of loopholes still remain that result in breaches.
LineageOS servers breached:
Well, many times we come across numerous instances about data cyber crimes and security breaches. Whether it is some hacker leaking private stuff or someone trying to steal something. There have been many breaches at the industry level as well that resulted in the leakage of data of all the people associated with it. There has been an immense rise in the number of such powerful hackers all around.
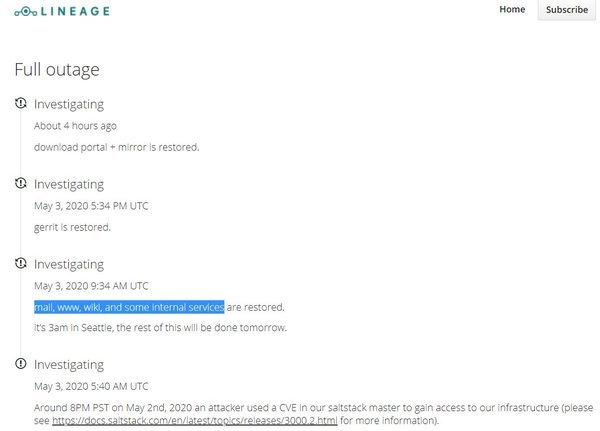
Popular Custom ROM LineageOS servers became the victim of a major breach this time. The news comes from yesterday(May 3, 2020). LineageOS is one of the most popular open-source community for custom ROMs. Some hackers breached their servers which rendered the full outage of LineageOS services. It’s still unknown what these hackers wanted? However, the LinagesOS team is consistently working to resume the services and many services are now up and running.
Around 8PM PST on May 2nd, 2020 an attacker used a CVE in our saltstack master to gain access to our infrastructure.
We are able to verify that:
– Signing keys are unaffected.
– Builds are unaffected.
– Source code is unaffected.See https://t.co/85fvp6Gj2h for more info.
— LineageOS (@LineageAndroid) May 3, 2020
According to the support, the attack was made using a CVE in the SaltStack master to gain access to the server’s infrastructure. In case you don’t know, SaltStack is a configuration management framework and orchestration tool. This further lets the system administrators automate server provisioning and task management. Given the fact that this is an open-source community, the CVE became publicly accessible a week ago. Hackers used this to gain access to LineageOS servers.
Current Status of Servers:
It is still pretty unclear why these hackers did this. Maybe they were trying to inject some malicious lines of code or perhaps not. That certainly is not the case because as revealed by the LinageOS team, the builds and source code are unaffected and the signing keys as well are intact. It is really peculiar why an open-source community became the target after all. It seems like all the services related to the websites only went on outage including updates.
After investigations, the team has now restored several services. This includes Gerrit, mail, www, wiki, and some internal services. The download portal and mirrors as well are now live and functioning. You can see the timeline of the server status of Lineage OS above. Well, not just LineageOS but hackers have been using this recent SaltStack CVE and trying to breach vulnerable servers as if it is a game.
While nothing seems to be wrong so far, a user says that after the server was up and running, the Nexus 5 is longer supported. But how is that even possible? Maybe some glitch, for now, we hope the LineageOS team to soon fox these issues and get all the services up and running in meanwhile. LineageOS was luckily not so late and now it seems like they will close all the publicly accessible Saltstakes.
Stay tuned for further updates on LineageOS breach and more such related content. Also, share its article with all those people who love using LineageOS.